How to use write_html_report method in autotest
Best Python code snippet using autotest_python
dpat.py
Source:dpat.py
...97 col_num += 198 html += "</tr>\n"99 html += "</table>"100 self.build_html_body_string(html)101 def write_html_report(self, filename):102 f = open(os.path.join(folder_for_html_report, filename), "w")103 copyfile(os.path.join(os.path.dirname(__file__), "report.css"), os.path.join(folder_for_html_report, "report.css"))104 f.write(self.get_html())105 f.close()106 return filename107hb = HtmlBuilder()108summary_table = []109summary_table_headers = ("Count", "Description", "More Info")110conn = sqlite3.connect(':memory:')111if args.writedb:112 if os.path.exists(filename_for_db_on_disk):113 os.remove(filename_for_db_on_disk)114 conn = sqlite3.connect(filename_for_db_on_disk)115if speed_it_up:116 conn = sqlite3.connect(filename_for_db_on_disk)117conn.text_factory = str118c = conn.cursor()119# nt2lmcrack functionality120# the all_casings functionality was taken from https://github.com/BBerastegui/foo/blob/master/casing.py121def all_casings(input_string):122 if not input_string:123 yield ""124 else:125 first = input_string[:1]126 if first.lower() == first.upper():127 for sub_casing in all_casings(input_string[1:]):128 yield first + sub_casing129 else:130 for sub_casing in all_casings(input_string[1:]):131 yield first.lower() + sub_casing132 yield first.upper() + sub_casing133def crack_it(nt_hash, lm_pass):134 password = None135 for pwd_guess in all_casings(lm_pass):136 hash = hashlib.new('md4', pwd_guess.encode('utf-16le')).hexdigest()137 if nt_hash.lower() == hash.lower():138 password = pwd_guess139 break140 return password141if not speed_it_up:142 # Create tables and indices143 c.execute('''CREATE TABLE hash_infos144 (username_full text collate nocase, username text collate nocase, lm_hash text, lm_hash_left text, lm_hash_right text, nt_hash text, password text, lm_pass_left text, lm_pass_right text, only_lm_cracked boolean, history_index int, history_base_username text)''')145 c.execute("CREATE INDEX index_nt_hash ON hash_infos (nt_hash);")146 c.execute("CREATE INDEX index_lm_hash_left ON hash_infos (lm_hash_left);")147 c.execute("CREATE INDEX index_lm_hash_right ON hash_infos (lm_hash_right);")148 c.execute("CREATE INDEX lm_hash ON hash_infos (lm_hash);")149 c.execute("CREATE INDEX username ON hash_infos (username);")150 # Create boolean column for each group151 for group in compare_groups:152 sql = "ALTER TABLE hash_infos ADD COLUMN \"" + group[0] + "\" boolean"153 c.execute(sql)154 # Read users from each group; groups_users is a dictionary with key = group name and value = list of users155 groups_users = {}156 for group in compare_groups:157 user_domain = ""158 user_name = ""159 try:160 users = []161 fing = io.open(group[1], encoding='utf-16')162 for line in fing:163 if "MemberDomain" in line:164 user_domain = (line.split(":")[1]).strip()165 if "MemberName" in line:166 user_name = (line.split(":")[1]).strip()167 users.append(user_domain + "\\" + user_name)168 except:169 print("Doesn't look like the Group Files are in the form output by PowerView, assuming the files are already in domain\\username list form")170 # If the users array is empty, assume the file was not in the PowerView PowerShell script output format that you get from running:171 # Get-NetGroupMember -GroupName "Enterprise Admins" -Domain "some.domain.com" -DomainController "DC01.some.domain.com" > Enterprise Admins.txt172 # You can list domain controllers for use in the above command with Get-NetForestDomain173 if len(users) == 0:174 fing = open(group[1])175 users = []176 for line in fing:177 users.append(line.rstrip("\n"))178 fing.close()179 groups_users[group[0]] = users180 # Read in NTDS file181 fin = open(ntds_file)182 for line in fin:183 vals = line.rstrip("\n").split(':')184 if len(vals) == 1:185 continue186 usernameFull = vals[0]187 lm_hash = vals[2]188 lm_hash_left = lm_hash[0:16]189 lm_hash_right = lm_hash[16:32]190 nt_hash = vals[3]191 username = usernameFull.split('\\')[-1]192 history_base_username = usernameFull193 history_index = -1194 username_info = r"(?i)(.*\\*.*)_history([0-9]+)$"195 results = re.search(username_info,usernameFull)196 if results:197 history_base_username = results.group(1)198 history_index = results.group(2)199 # Exclude machine accounts (where account name ends in $) by default200 if args.machineaccts or not username.endswith("$"):201 c.execute("INSERT INTO hash_infos (username_full, username, lm_hash , lm_hash_left , lm_hash_right , nt_hash, history_index, history_base_username) VALUES (?,?,?,?,?,?,?,?)",202 (usernameFull, username, lm_hash, lm_hash_left, lm_hash_right, nt_hash, history_index, history_base_username))203 fin.close()204 # update group membership flags205 for group in groups_users:206 for user in groups_users[group]:207 sql = "UPDATE hash_infos SET \"" + group + \208 "\" = 1 WHERE username_full = \"" + user + "\""209 c.execute(sql)210 # read in POT file211 fin = open(cracked_file)212 for lineT in fin:213 line = lineT.rstrip('\r\n')214 colon_index = line.find(":")215 hash = line[0:colon_index]216 # Stripping $NT$ and $LM$ that is included in John the Ripper output by default217 jtr = False218 if hash.startswith('$NT$') or hash.startswith('$LM$'):219 hash = hash.lstrip("$NT$")220 hash = hash.lstrip("$LM$")221 jtr = True222 password = line[colon_index+1:len(line)]223 lenxx = len(hash)224 if re.match(r"\$HEX\[([^\]]+)", password) and not jtr:225 hex2 = (binascii.unhexlify(re.findall(r"\$HEX\[([^\]]+)", password)[-1]))226 l = list()227 for x in list(hex2):228 if type(x) == int:229 x = str(chr(x))230 l.append(x)231 password = ""232 password = password.join(l)233 if lenxx == 32: # An NT hash234 c.execute("UPDATE hash_infos SET password = ? WHERE nt_hash = ?", (password, hash))235 elif lenxx == 16: # An LM hash, either left or right236 c.execute("UPDATE hash_infos SET lm_pass_left = ? WHERE lm_hash_left = ?", (password, hash))237 c.execute("UPDATE hash_infos SET lm_pass_right = ? WHERE lm_hash_right = ?", (password, hash))238 fin.close()239 # Do additional LM cracking240 c.execute('SELECT nt_hash,lm_pass_left,lm_pass_right FROM hash_infos WHERE (lm_pass_left is not NULL or lm_pass_right is not NULL) and password is NULL and lm_hash is not "aad3b435b51404eeaad3b435b51404ee" group by nt_hash')241 list = c.fetchall()242 count = len(list)243 if count != 0:244 print("Cracking %d NT Hashes where only LM Hash was cracked (aka lm2ntcrack functionality)" % count)245 for pair in list:246 lm_pwd = ""247 if pair[1] is not None:248 lm_pwd += pair[1]249 if pair[2] is not None:250 lm_pwd += pair[2]251 password = crack_it(pair[0], lm_pwd)252 if password is not None:253 c.execute('UPDATE hash_infos SET only_lm_cracked = 1, password = \'' + password.replace("'", "''") + '\' WHERE nt_hash = \'' + pair[0] + '\'')254 count -= 1255# Total number of hashes in the NTDS file256c.execute('SELECT username_full,password,LENGTH(password) as plen,nt_hash,only_lm_cracked FROM hash_infos WHERE history_index = -1 ORDER BY plen DESC, password')257list = c.fetchall()258num_hashes = len(list)259hbt = HtmlBuilder()260hbt.add_table_to_html(261 list, ["Username", "Password", "Password Length", "NT Hash", "Only LM Cracked"])262filename = hbt.write_html_report("all hashes.html")263summary_table.append((num_hashes, "Password Hashes",264 "<a href=\"" + filename + "\">Details</a>"))265# Total number of UNIQUE hashes in the NTDS file266c.execute('SELECT count(DISTINCT nt_hash) FROM hash_infos WHERE history_index = -1')267num_unique_nt_hashes = c.fetchone()[0]268summary_table.append((num_unique_nt_hashes, "Unique Password Hashes", None))269# Number of users whose passwords were cracked270c.execute('SELECT count(*) FROM hash_infos WHERE password is not NULL AND history_index = -1')271num_passwords_cracked = c.fetchone()[0]272summary_table.append(273 (num_passwords_cracked, "Passwords Discovered Through Cracking", None))274# Number of UNIQUE passwords that were cracked275c.execute(276 'SELECT count(Distinct password) FROM hash_infos where password is not NULL AND history_index = -1 ')277num_unique_passwords_cracked = c.fetchone()[0]278summary_table.append((num_unique_passwords_cracked,279 "Unique Passwords Discovered Through Cracking", None))280# Percentage of current passwords cracked and percentage of unique passwords cracked281percent_cracked_unique = num_unique_passwords_cracked / \282 float(num_unique_nt_hashes)*100283percent_all_cracked = num_passwords_cracked/float(num_hashes)*100284summary_table.append(("%0.1f" % percent_all_cracked,285 "Percent of Current Passwords Cracked", "<a href=\"" + filename + "\">Details</a>"))286summary_table.append(("%0.1f" % percent_cracked_unique,287 "Percent of Unique Passwords Cracked", "<a href=\"" + filename + "\">Details</a>"))288# Group Membership Details and number of passwords cracked for each group289for group in compare_groups:290 c.execute(291 "SELECT username_full,nt_hash FROM hash_infos WHERE \"" + group[0] + "\" = 1 AND history_index = -1")292 # this list contains the username_full and nt_hash of all users in this group293 list = c.fetchall()294 num_groupmembers = len(list)295 new_list = []296 for tuple in list: # the tuple is (username_full, nt_hash, lm_hash)297 c.execute(298 "SELECT username_full FROM hash_infos WHERE nt_hash = \"" + tuple[1] + "\" AND history_index = -1")299 users_list = c.fetchall()300 if len(users_list) < 30:301 string_of_users = (', '.join(''.join(elems)302 for elems in users_list))303 new_tuple = tuple + (string_of_users,)304 else:305 new_tuple = tuple + ("Too Many to List",)306 new_tuple += (len(users_list),)307 c.execute(308 "SELECT password,lm_hash FROM hash_infos WHERE nt_hash = \"" + tuple[1] + "\" AND history_index = -1 LIMIT 1")309 result = c.fetchone()310 new_tuple += (result[0],)311 # Is the LM Hash stored for this user?312 if result[1] != "aad3b435b51404eeaad3b435b51404ee":313 new_tuple += ("Yes",)314 else:315 new_tuple += ("No",)316 new_list.append(new_tuple)317 headers = ["Username", "NT Hash", "Users Sharing this Hash",318 "Share Count", "Password", "Non-Blank LM Hash?"]319 hbt = HtmlBuilder()320 hbt.add_table_to_html(new_list, headers)321 filename = hbt.write_html_report(group[0] + " members.html")322 summary_table.append((num_groupmembers, "Members of \"%s\" group" %323 group[0], "<a href=\"" + filename + "\">Details</a>"))324 c.execute("SELECT username_full, LENGTH(password) as plen, password, only_lm_cracked FROM hash_infos WHERE \"" +325 group[0] + "\" = 1 and password is not NULL and password is not '' ORDER BY plen")326 group_cracked_list = c.fetchall()327 num_groupmembers_cracked = len(group_cracked_list)328 headers = ["Username of \"" + group[0] + "\" Member",329 "Password Length", "Password", "Only LM Cracked"]330 hbt = HtmlBuilder()331 hbt.add_table_to_html(group_cracked_list, headers)332 filename = hbt.write_html_report(group[0] + " cracked passwords.html")333 summary_table.append((num_groupmembers_cracked, "\"%s\" Passwords Cracked" %334 group[0], "<a href=\"" + filename + "\">Details</a>"))335# Number of LM hashes in the NTDS file, excluding the blank value336c.execute('SELECT count(*) FROM hash_infos WHERE lm_hash is not "aad3b435b51404eeaad3b435b51404ee" AND history_index = -1')337summary_table.append((c.fetchone()[0], "LM Hashes (Non-blank)", None))338# Number of UNIQUE LM hashes in the NTDS, excluding the blank value339c.execute('SELECT count(DISTINCT lm_hash) FROM hash_infos WHERE lm_hash is not "aad3b435b51404eeaad3b435b51404ee" AND history_index = -1')340summary_table.append((c.fetchone()[0], "Unique LM Hashes (Non-blank)", None))341# Number of passwords that are LM cracked for which you don't have the exact (case sensitive) password.342c.execute('SELECT lm_hash, lm_pass_left, lm_pass_right, nt_hash FROM hash_infos WHERE (lm_pass_left is not "" or lm_pass_right is not "") AND history_index = -1 and password is NULL and lm_hash is not "aad3b435b51404eeaad3b435b51404ee" group by lm_hash')343list = c.fetchall()344num_lm_hashes_cracked_where_nt_hash_not_cracked = len(list)345output = "WARNING there were %d unique LM hashes for which you do not have the password." % num_lm_hashes_cracked_where_nt_hash_not_cracked346if num_lm_hashes_cracked_where_nt_hash_not_cracked != 0:347 hbt = HtmlBuilder()348 headers = ["LM Hash", "Left Portion of Password",349 "Right Portion of Password", "NT Hash"]350 hbt.add_table_to_html(list, headers)351 filename = hbt.write_html_report("lm_noncracked.html")352 hb.build_html_body_string(353 output + ' <a href="' + filename + '">Details</a>')354 output2 = "</br> Cracking these to their 7-character upcased representation is easy with Hashcat and this tool will determine the correct case and concatenate the two halves of the password for you!</br></br> Try this Hashcat command to crack all LM hashes:</br> <strong>./hashcat64.bin -m 3000 -a 3 customer.ntds -1 ?a ?1?1?1?1?1?1?1 --increment</strong></br></br> Or for John, try this:</br> <strong>john --format=LM customer.ntds</strong></br>"355 hb.build_html_body_string(output2)356# Count and List of passwords that were only able to be cracked because the LM hash was available, includes usernames357c.execute('SELECT username_full,password,LENGTH(password) as plen,only_lm_cracked FROM hash_infos WHERE only_lm_cracked = 1 ORDER BY plen AND history_index = -1')358list = c.fetchall()359hbt = HtmlBuilder()360headers = ["Username", "Password", "Password Length", "Only LM Cracked"]361hbt.add_table_to_html(list, headers)362filename = hbt.write_html_report("users_only_cracked_through_lm.html")363summary_table.append((len(list), "Passwords Only Cracked via LM Hash",364 "<a href=\"" + filename + "\">Details</a>"))365c.execute('SELECT COUNT(DISTINCT nt_hash) FROM hash_infos WHERE only_lm_cracked = 1 AND history_index = -1')366summary_table.append(367 (c.fetchone()[0], "Unique LM Hashes Cracked Where NT Hash was Not Cracked", None))368# Password length statistics369c.execute('SELECT LENGTH(password) as plen,COUNT(password) FROM hash_infos WHERE plen is not NULL AND history_index = -1 AND plen is not 0 GROUP BY plen ORDER BY plen')370list = c.fetchall()371counter = 0372for tuple in list:373 length = str(tuple[0])374 c.execute('SELECT username FROM hash_infos WHERE history_index = -1 AND LENGTH(password) = ' + length)375 usernames = c.fetchall()376 hbt = HtmlBuilder()377 headers = ["Users with a password length of " + length]378 hbt.add_table_to_html(usernames, headers)379 filename = hbt.write_html_report(str(counter) + "length_usernames.html")380 list[counter] += ("<a href=\"" + filename + "\">Details</a>",)381 counter += 1382hbt = HtmlBuilder()383headers = ["Password Length", "Count", "Details"]384hbt.add_table_to_html(list, headers, 2)385c.execute('SELECT COUNT(password) as count, LENGTH(password) as plen FROM hash_infos WHERE plen is not NULL AND history_index = -1 and plen is not 0 GROUP BY plen ORDER BY count DESC')386list = c.fetchall()387headers = ["Count", "Password Length"]388hbt.add_table_to_html(list, headers)389filename = hbt.write_html_report("password_length_stats.html")390summary_table.append((None, "Password Length Stats",391 "<a href=\"" + filename + "\">Details</a>"))392# Top Ten Passwords Used393c.execute('SELECT password,COUNT(password) as count FROM hash_infos WHERE password is not NULL AND history_index = -1 and password is not "" GROUP BY password ORDER BY count DESC LIMIT 20')394list = c.fetchall()395hbt = HtmlBuilder()396headers = ["Password", "Count"]397hbt.add_table_to_html(list, headers)398filename = hbt.write_html_report("top_password_stats.html")399summary_table.append((None, "Top Password Use Stats",400 "<a href=\"" + filename + "\">Details</a>"))401# Password Reuse Statistics (based only on NT hash)402c.execute('SELECT nt_hash, COUNT(nt_hash) as count, password FROM hash_infos WHERE nt_hash is not "31d6cfe0d16ae931b73c59d7e0c089c0" AND history_index = -1 GROUP BY nt_hash ORDER BY count DESC LIMIT 20')403list = c.fetchall()404counter = 0405for tuple in list:406 c.execute(407 'SELECT username FROM hash_infos WHERE nt_hash = \"' + tuple[0] + '\" AND history_index = -1')408 usernames = c.fetchall()409 password = tuple[2]410 if password is None:411 password = ""412 hbt = HtmlBuilder()413 headers = ["Users Sharing a hash:password of " +414 sanitize(tuple[0]) + ":" + sanitize(password)]415 hbt.add_table_to_html(usernames, headers)416 filename = hbt.write_html_report(str(counter) + "reuse_usernames.html")417 list[counter] += ("<a href=\"" + filename + "\">Details</a>",)418 counter += 1419hbt = HtmlBuilder()420headers = ["NT Hash", "Count", "Password", "Details"]421hbt.add_table_to_html(list, headers, 3)422filename = hbt.write_html_report("password_reuse_stats.html")423summary_table.append((None, "Password Reuse Stats",424 "<a href=\"" + filename + "\">Details</a>"))425# Password History Stats426c.execute('SELECT MAX(history_index) FROM hash_infos;')427max_password_history = c.fetchone()428max_password_history = max_password_history[0]429hbt = HtmlBuilder()430if max_password_history < 0:431 hbt.build_html_body_string("There was no history contained in the password files. If you would like to get the password history, run secretsdump.py with the flag \"-history\". <br><br> Sample secretsdump.py command: secretsdump.py -system registry/SYSTEM -ntds \"Active Directory/ntds.dit\" LOCAL -outputfile customer -history")432else:433 password_history_headers = ["Username", "Current Password"]434 column_names = ["cp"]435 command = 'SELECT * FROM ( '436 command += 'SELECT history_base_username'437 for i in range(-1,max_password_history + 1):438 if i == -1:439 column_names.append("cp")440 else:441 password_history_headers.append("History " + str(i))442 column_names.append("h" + str(i))443 command += (', MIN(CASE WHEN history_index = ' + str(i) + ' THEN password END) ' + column_names[-1])444 command += (' FROM hash_infos GROUP BY history_base_username) ')445 command += "WHERE coalesce(" + ",".join(column_names) + ") is not NULL"446 c.execute(command)447 list = c.fetchall()448 headers = password_history_headers449 hbt.add_table_to_html(list, headers, 8)450filename=hbt.write_html_report("password_history.html")451summary_table.append((None, "Password History",452 "<a href=\"" + filename + "\">Details</a>"))453# Write out the main report page454hb.add_table_to_html(summary_table, summary_table_headers, 2)455hb.write_html_report(filename_for_html_report)456print("The Report has been written to the \"" + filename_for_html_report +457 "\" file in the \"" + folder_for_html_report + "\" directory")458# Save (commit) the changes and close the database connection459conn.commit()460conn.close()461try:462 input = raw_input463except NameError:464 pass465# prompt user to open the report466# the code to prompt user to open the file was borrowed from the EyeWitness tool https://github.com/ChrisTruncer/EyeWitness467print('Would you like to open the report now? [Y/n]')468while True:469 try:...generate_report_spa.py
Source:generate_report_spa.py
...5def write_html_report_for_spa(date_range):6 out_dir = config.HTML_REPORTS_DIR7 out_dir.mkdir(exist_ok=True)8 out_path = out_dir / f'situacion_covid_spa.html'9 write_html_report(out_path, spa_report=True, date_range=date_range)10if __name__ == '__main__':11 ten_days_ago = datetime.datetime.now() - datetime.timedelta(days=10)12 forty_days_ago = datetime.datetime.now() - datetime.timedelta(days=40)13 first_date = datetime.datetime(2020, 9, 1)...Automation Testing Tutorials
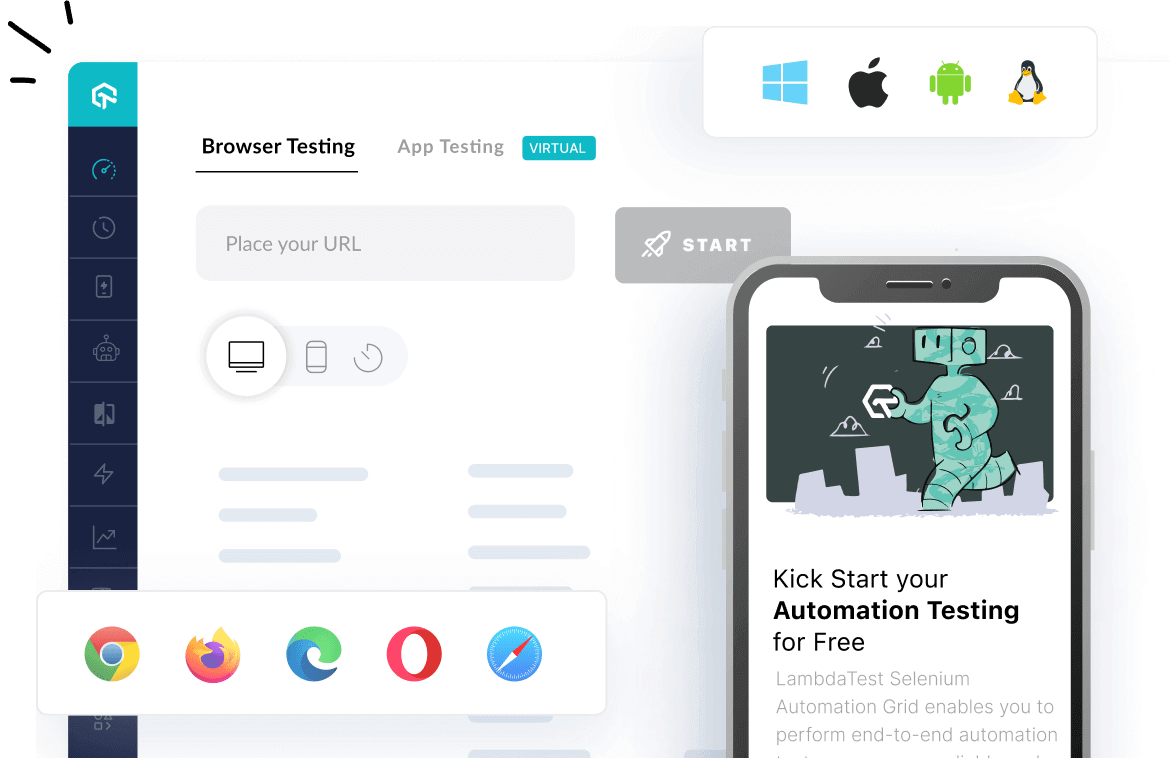
Learn to execute automation testing from scratch with LambdaTest Learning Hub. Right from setting up the prerequisites to run your first automation test, to following best practices and diving deeper into advanced test scenarios. LambdaTest Learning Hubs compile a list of step-by-step guides to help you be proficient with different test automation frameworks i.e. Selenium, Cypress, TestNG etc.
LambdaTest Learning Hubs:
- JUnit Tutorial
- TestNG Tutorial
- Webdriver Tutorial
- WebDriverIO Tutorial
- Protractor Tutorial
- Selenium 4 Tutorial
- Jenkins Tutorial
- NUnit Tutorial
- Jest Tutorial
- Playwright Tutorial
- Cypress Tutorial
- PyTest Tutorial
YouTube
You could also refer to video tutorials over LambdaTest YouTube channel to get step by step demonstration from industry experts.
Try LambdaTest Now !!
Get 100 minutes of automation test minutes FREE!!